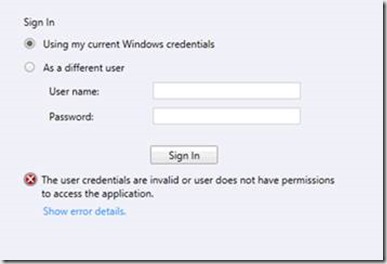
When accessing the web console from the server hosting the web site there is no problem, but when accessing it from another server, you get the following message:
This issue is pretty common and I have already blogged about it here: https://blog.ctglobalservices.com/msk/scom-2012-web-console-prompts-for-username-and-password/. As written in the blog post, this is due to Kerberos double hop.
But what to do when that solution doesn’t do the trick?
I made sure that everything was as supposed:
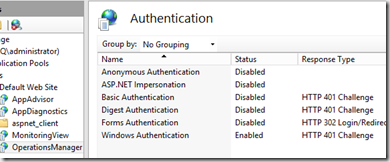
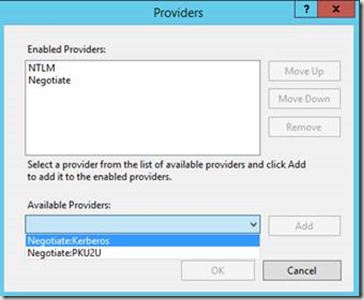
Only Windows Authentication was enabled:
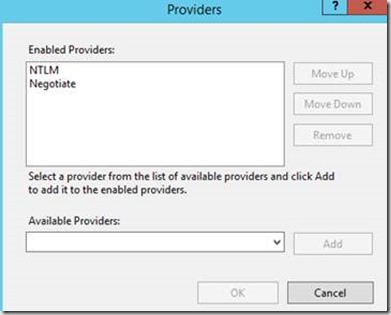
In Providers, NTLM had been moved up, which normally is the fix:
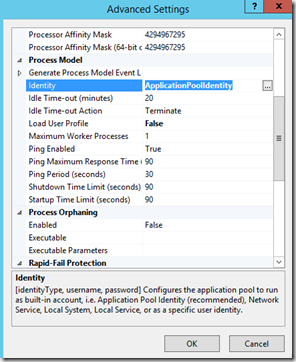
I then started looking at the Advanced Settings of the Application Pool and even tried to change the identity to Local System, SDK etc. – no luck.
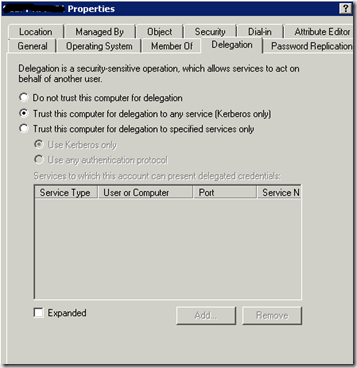
Several places I read about a setting in Active Directory: ”Trust this computer for delegation to any service (Kerberos only)”:
But this had no affect either. I also read that one must choose the last option if the Domain Functional Level is 2003, which wasn’t my case.
Solution
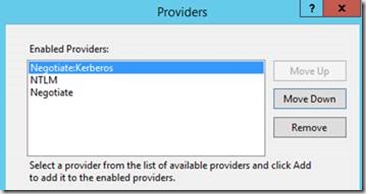
I had compared every value with my own environment and everything was exactly the same. Except for one. In Providers I saw the “Available Providers” and found “Negotitate:Kerberos”, which sounded like something I needed.
I added this and moved it up.
Voila! I am now able to open the web console on any server without being asked for credentials!
Happy accessing your web console without typing in your credentials!
Nice to see your solution. I’m planning the same. I wonder if this will also work *without* the “Trust this computer for delegation” setting in AD…
Hi Yin
I am pretty sure it will work without. I have only had the need to set the trust a couple of times when dealing with this.
Thanks
Michael
I have also added “Negotiatate:Kerberos” to MonitoringView website, because without it I couldn’t see any of views in console (500 – Internal server error)
Thank You for this solution 🙂
This solution did not work for me. When we access the SCOM console, we are prompted for user name and password. Once entered, we can get in to the console, but when I click on an alert view I get a 500 Error. However, if I click ‘Sign Out’ and then sign back in I dont have any issues at all.
Hi, what worked for me was changed ntlm to be the top provider for BOTH the OperationsManager AND MonitoringView IIS websites. Once I made this change on the MonitoringView website everything started working.
Changing NTLM to be the top provider for BOTH the OperationsManager AND MonitoringView IIS websites worked for me too. Adding Negotiate:Kerberos produced warning “…cannot be used when kernal mode authentication is enabled..” so I didn’t bother.
Carl says:
9th Oct 2014 at 02:15
Hello Carl , You Are A Star your solution worked like a charm in my case, You Saved My Day God Bless You
Changing ntlm to be the top provider for both the OperationsManager and MonitoringView IIS websites also worked for me. Thanks!
Just something to note, by moving NTLM to the top of the providers list, authentication is performed using NTLM rather than Kerberos.
I too had this issue, and spent some time working through it. I suspect the underlying reason why it works after adding the additional provider is that kernel mode authentication has now been disabled. As mentioned by Paul, after adding in Negotiate:Kerberos, there’s is a warning about compatibility with the provider and kernel mode authentication. I’ve tested it, and just simply disabling Kernel mode authentication works without adding or changing provider order. This is after allowing Kerberos delegation in AD for the Web Console computer object.
As I wished to avoid disabling kernel mode authentication altogether, I eventually figured out the necessary setting for Kerberos based pass through authentication.
Using the IIS Manager console, I went to the /OperationsManager and /MonitoringView folders. For each both applications, I opened the Configuration Editor and changed the drop down settings for Section to “system.webServer/security/authentication/windowsAuthentication” and From to “ApplicationHost.config …”
From there, I set the value of useAppPoolCredentials to true and applied the settings. And that was it, after restarting IIS, the web console launched successfully.
| July 3rd, 2009 993850 457524Oh my goodness! a amazing write-up dude. Thanks a good deal Nonetheless We are excerienping trouble with ur rss . Do not know why Not able to sign up to it. Possibly there is anybody finding identical rss dilemma? Anyone who knows kindly respond. Thnkx 623868
You underestimate the moslem’s attachment to occupied Jesuralem. You also forget that both Iran and the hiz, by their own admission, are supplying Gaza with defensive weapons whenever they can.There is nothing more powerfully symbolic for Arabs and moslems than the liberation of Jerusalem and the holy lands.Iran and Lebanon are blatant supporters of Palestinian resistance. No ifs and buts about it.
Not sure this is the right place to ask, so bear with me.
We have a wall display showing the status of our Nagios and SCOM installation in iFrames.
It is running on a thinclient running CentOS so it’s not part of any AD domain.
What we would like, was to set this computer to shutdown at 18 og wakeup at 7, booting right to firefox or chrome with our iFrame page, without any user intervention.
Nagios, being served by apache, accepts the in-url-encoded-auth like “https://readonly:readonly@nagios.domain.com” but SCOM (or IIS is suppose) won’t accept authentication in the URL.
Do any or you cleaver people have a suggestion to work around this?
I had this problem. I tried everything suggested on here but none of it worked. I eventually found this page:
https://blogs.technet.microsoft.com/momteam/2008/01/30/running-the-web-console-server-on-a-standalone-server-using-windows-authentication/
It’s outdated but still applies to an extent. The following is what worked for me:
My Operations Web Console is on a separate server to the rest of SCOM. I had already added the SCOMSdkSvc SPNs using both NETBIOS name and FQDN of the management servers to the SDK account. I then went to the AD account of the server running the web console, went to the delegation tab and chose “Trust this computer for delegation to specified services only”. I selected “Use any authentication protocol” and pressed the Add button. I put in the SDK service account and chose the two SPNs that appeared.
With all that in, the OpsMgr web console is now automatically authenticating.
Hi Folks,
My web console is on database server. SSO is not working for me. I have tried all the steps mentioned above. Could someone help me to get it resolved.
Thanks,
Aditya Deo
Hi.
SCOM2012R2 do as described above, but do not get access to the web console.
Restart web-server needed?