This guide is written by Panu Saukko and Kent Agerlund (both Microsoft Enterprise Client MVP’s). These are the steps we used in our demo environments to configure the new on-prem MDM feature in system Center Configuration Manager vNext Technical Preview 3. In the article you will notice that we used two different environments and you will see screenshots from both environments. Don’t let that confuse you, happy reading and enrolling.
The environments we used are:
Configuration Manager site: vn3, Site Server: vnext.corp.viamonstra.com, Domain: corp.viamonstra.com, PKI server: dc.corp.viamonstra.com
Configuration Manager site: C15, Domain: cmdemo.local, PKI server: cm-dc1.cmdemo.local
System Center 2012 Configuration Manager has an option to manage mobile devices using Microsoft Intune. The feature requires that mobile devices must have an internet access which is sometimes not an option for the organization.
In ConfigMgr vNext we now have an option to manage mobile devices using on-prem environment. The feature is not fully ready and have some limitations like:
- Currently only Windows 10 devices are supported
- This still requires Microsoft Intune subscription, which is needed for accounting purposes. The mobile devices don’t contact Intune services, so they don’t need to have an internet connection (well almost not, please see the troubleshooting section for more information).
The infrastructure requirements
The infrastructure requirements can be quite tricky due to the fact that you need at least one HTTPS based management point, distribution point and enrollment point. If your environment has an internal Certificate Authority (CA) hierarchy, then you can utilize that and just go ahead with creating the certificates. The challenge for many is if you don’t have CAs. In that case you need to install and configure at least one CA server. The PKI requirements are described in the TechNet documentation https://technet.microsoft.com/en-us/library/gg699362.aspx.
For Configuring a POC environment, you can also do the cool thing and let PowerShell configure your PKI server. This example will install and configure PKI:
Add-WindowsFeature Adcs-Cert-Authority -IncludeManagementTools
Add-WindowsFeature Adcs-Enroll-Web-Svc -IncludeAllSubFeature -IncludeManagementTools
Add-WindowsFeature ADCS-Web-Enrollment -IncludeAllSubFeature -IncludeManagementTools
Install-AdcsCertificationAuthority -CAType EnterpriseRootCA -CryptoProviderName "RSA#Microsoft Software Key Storage Provider" -ValidityPeriod Years -ValidityPeriodUnits 5 -KeyLength 2048 -HashAlgorithmName SHA1 -Force
Install-AdcsWebEnrollment –Force
After that next step is to configure and deploy the certificates. Step-by-Step Example Deployment of the PKI Certificates for Configuration Manager: Windows Server 2008 Certification Authority: https://technet.microsoft.com/en-us/library/gg682023.aspx in our demo environment we configured 1 web server certificate and 1 Client certificate.
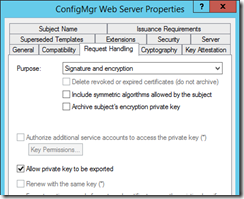
The ConfigMgr Web Server certificate, where we included both Server Authentication and Client Authentication. The certificate is based on the web server template. On the Request handling tab configure the Allow private key to be exported and ensure the site system servers can read and enroll the certificate.
One very important step that is missing from the TechNet documentation is the configuration of the Certificate Revocation Lists (CRLs). You must configure Certificate Revocation Lists (CRLs) otherwise the Windows 10 device enrollment process will fail. The Windows 10 MDM client will automatically do CRL checking, a “feature” which you cannot disable. Here is a link to the good article how to configure CRLs to a local server:
- These are the steps we followed to configure CRL:
- Create the directory c:\inetpub\wwwroot\certenroll
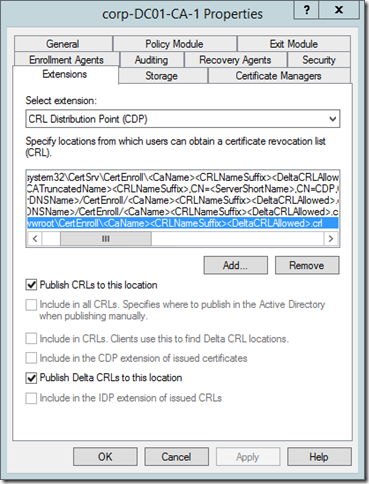
- Launch the Certification Authority, right click the properties and select the Extensions tab.
- Click Add and configure the URL to the CRL folder, in our example it is c:\inetpub\wwwroot\certenroll\<CaName><CRLNameSuffix><DeltaCRLAllowed>.crl. In Variable select <DeltaCRLAllowed> and click OK.
- Make sure you enable Publish CRLs to this location and Publish Delta CRLs to this location and click OK.
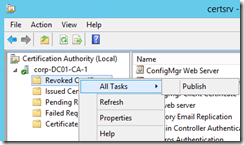
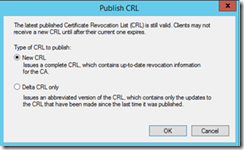
- Right click Revoked certificates, All Tasks and click Publish.
- Select New URL and click OK.
- These are the publishing parameters we used:
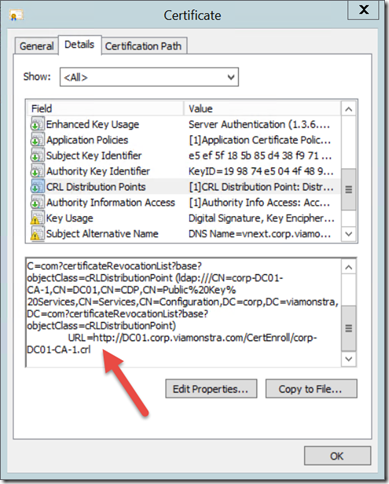
After publishing the certificates, you need to verify that certificate(s) used by the management point and distribution point is configured to use the CRL. After you have enrolled the certificate, open the certificate properties, click Details and check the CRL Distribution Points.
From the CRL Distribution Points properties, copy the URL (in this example http://DC01.corp.viamonstra.com/CertEnroll/corp-DC01-CA-1.crl) and paste it into to your favorite web browser. Also, check that you can access the delta CRL which is typically the same file name appended with “+” character (http://DC01.corp.viamonstra.com/CertEnroll/corp-DC01-CA-1+.crl). Remember that you need to enable allowDoubleEscaping setting to allow IIS to support URLs with “+” characters.
Configuration Manager Configurations
On ConfigMgr side, you must enable User Discovery. Create a user collection which contains the users who are allowed to enroll mobile devices:
Then restart the SMS_Certificate_Manager thread of the SMS_Executive service.
If your site server is running on Windows Server 2012 R2, create and set the following registry key value as a DWORD, on the site server:
HKLM/system/currentcontrolset/control/securityproviders/schannel/SendTrustedIssuerList=1
On ConfigMgr configure the following site servers:
- Cloud connection point: to provide connection to Microsoft Intune
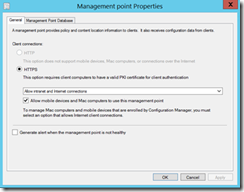
- HTTPS enabled MP, enable: Allow mobile devices and Mac computers to use this management setting
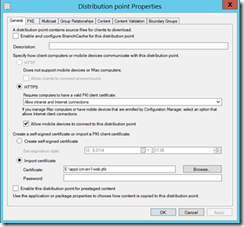
- HTTPS enabled DP with the following setting enabled: Allow mobile devices to connect to this distribution point
- Enrollment Point with standard settings
- Enrollment Proxy Point with standard settings
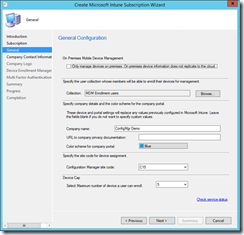
When you add Microsoft Intune subscription to ConfigMgr you can select: Only manage devices on premises if you don’t select it, the same Intune tenant can manage both on-prem and cloud based mobile devices. On-prem MDM management doesn’t require any special configuration to Microsoft Intune. For example, you don’t need to configure Azure Active Directory like you normally need when managing devices over the Internet.
When adding Microsoft Intune connection, define a collection of users who are allowed to enroll devices.
Remember to select Configure Platforms / Windows / Enable Windows enrollment to allow enrollment of Windows devices.
Prepare the Windows 10 devices
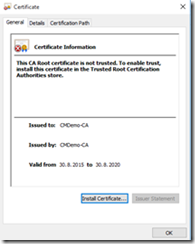
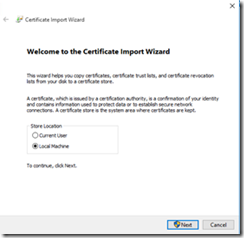
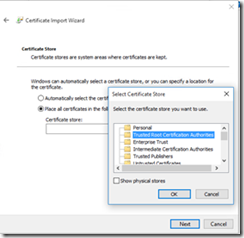
Windows 10 devices that will be enrolled to on-prem MDM need to trust the CA’s root certificate. You have a couple of options to do that.
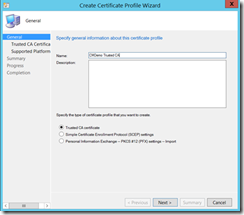
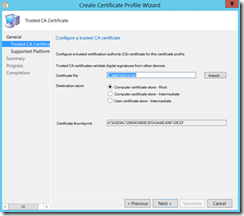
First you need to export the CA’s certificate to .cer file. Then you can import the certificate to ConfigMgr. In the ConfigMgr console, go to Assets and Compliance / Compliance Settings / Company Resource Access / Certificate Profiles. Click Create Certificate Profile and name to the profile, make sure that Trusted CA certificate is selected.
On the Trusted CA Certificate page, click Import and browse to the root cer file, and select Computer certificate store – Root as the destination store.
The last step is to enable Windows 10 as a supported platform.
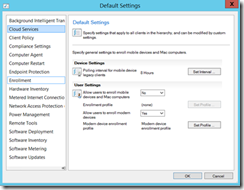
Next step is to create the Modern device enrollment profile in the client settings. From the administration workspace, open the Default Client Setting properties.
The creation of the profile is easy. Just give a name, select the management point site code, and you should see the certificate profile that you created earlier.
In Technical Preview 3, there seems to be a bug that the root certificate defined in Modern device enrollment profile is not correctly installed to the client. Thus, you need to manually add CA’s certificate to the client’s Trusted Root Certification Store or you can create an enrollment profile.
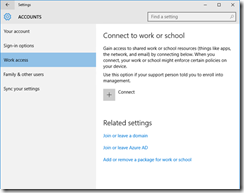
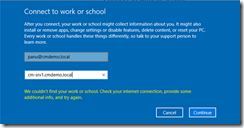
The enrollment is quite easy on Windows 10. First you need to go to Settings / Accounts / Work access and select Connect.
Then you provide your account’s UPN. First it will fail, because you need to enter your Enrollment Proxy Point’s FQDN:
Then you just enter the password and if everything is fine, you should see the following message:
As you can see, there are quite a few steps to make on-prem MDM to work!
Troubleshooting tips
If the enrollment doesn’t work, check the following things:
- Is the name resolution working? Can you resolve your server’s FQDN from Windows 10 client?
- You get a nice error message, if Windows 10 client doesn’t trust the MPs certificate. Then you need to import your CAs certificate to your client’s Trust Root Certificate store.
If you can enroll Windows 10 machine successfully, but it cannot sync correctly with the error 0x800728f, check your CRL settings.
Most probably, you cannot either access the CRL or delta CRL file from Windows 10 client.
Here are some useful log files on management point that you should check if you have problems:
EnrollmentService.log (\sms_ccm\EnrollmentPoint\Log)
If you don’t have Intune connection correctly, you might see the following error:
Error reading tenant ID from database. No account ID. Probably Intune subscription haven’t finished setup
SMS_DM (\sms_ccm\logs)
Gives you information about mobile device management point.
For this release, Internet access is required for the client policy synchronization to work. Without Internet connection you can enroll the device but synchronization fails.
About the Authors:
Panu Saukko, Enterprise Client Management MVP and MCT, is a senior consultant and trainer ProTrainIT with more than 20 years of experience working with Microsoft technologies. He has been MVP since 2003.
Twitter: @panusaukko
Kent Agerlund, Enterprise Client Management MVP, is chief enterprise client management architect @ Coretech Global and trainer with more than 20 years of experience working with Microsoft technologies.
Twitter: @Agerlund









Great article!
Unfortunately, I’m not able to enroll my Windows 10 machine. I’m getting the error “Something went wrong…” on the last step…after entering my credentials on the “Connecting to a service” screen. Any thoughts on this?
Regards
Martin
It’s finally working. The Default Client Settings prevents the Enrollment 🙂
[…] blog post on how to get started with On-Prem MDM in Configuration Manager vNext Technical Preview, http://blog.coretech.dk/kea/install-and-configure-on-prem-mobile-device-management-mdm-with-configmg… I had the same issue as they are explaining as well that my CRL lists where not accessible to […]
Great post,
for me however, the “Only manage devices on premises” option does not appear in the wizard.
I have upgraded to 1510 and have not tried before so can’t tell if that would make the difference.
Is there anything to configure on the Intune account – would be good to have a description when working with a trial intune account.
Cheers
Kris
Is it in the Intune connector wizard?
Sorry for the late reply: yes, I meant that. Then option that appears on your screenshot is simply missing for me. So that is why I mentioned I’m using a trial account, not sure if that counts.
Under MDM there are many solutions such as company cell phone devices management, cell phone insurance, wireless support, and many more to save the time and hundreds of dollar monthly.