Many people who know me know that I am not the fan boy of Android devices. It can be a nightmare when managing those devices, but is that still a valid statement or is it getting better? In this series of blogs, I want to try to get a clear view if Android devices in an Enterprise are a blessing or a nightmare. That there are Android devices connecting to most environments to get access to corporate data is a fact. When looking at Microsoft Intune we can block the ability that Android devices can be enrolled into Intune, but is that what we really want?
Managing (legacy) Androids the MDM way
Managing a subset of those over 24.000 different Android devices is a huge challenge. If you support Android in your environment then you basically need to support all those different flavors or you need to scope it down to certain versions via the enrollment restrictions.
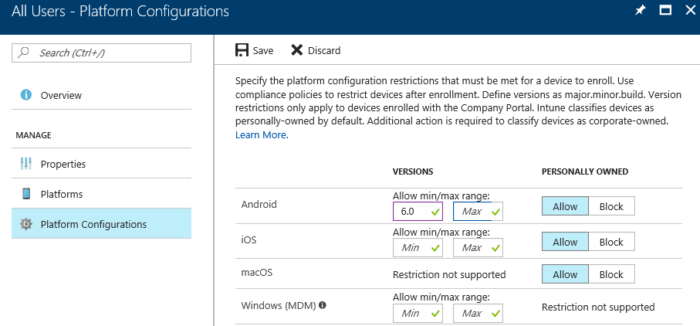
If a user enrolls their device in Intune via the Intune Company Portal, the company portal will be granted full permissions to the phone. The company portal or a remote Administrator can perform for instance a full wipe, change the screen lock, change password rules, lock the screen, enforce device encryption and more, even making phone calls. Yes phone calls, apparently there is no management API within Android that is exposing the EMEI number for MDM vendors like Microsoft. You don’t need to be afraid that the Intune Company Portal will make phone calls on your behalf, they won’t! The API is only used to get the inventory data.
The platform Android is great if you like the openness of the platform, developing your own apps and publish them via the Play Store or any other app store is easy. So easy that a lot of malicious apps are available in the different app stores. Last year I wrote a blog about the fact that Google was removing the ability for MDMs in Android 7.0+ to reset the passcodes on the devices. The reason behind the removal of this feature from the API was that malicious ransomware apps were misusing this feature to hijack the device by changing the passcode. After the user payed the ransom the user got access to the device again.
To install apps from other app stores than the Google Play store you need to enable a feature called install apps from unknown sources. The fact that the ability to install apps from unknown sources cannot be disabled is a risk, basically what it means is when you enable this feature is that you can install any app from any other (dodgy) app store there is.
Besides the apps Android does not expose a lot of controls for MDM vendors to let them secure the devices and Google is not investing in expanding the capabilities on Android itself. For that reason, Samsung created Samsung Knox and Samsung Save to give enterprises more control to lock down the devices, besides Samsung also other vendors like LG, Sony, Intel, Asus and more are creating custom controls. Not an ideal solution if you ask me, all vendors doing their own thing in this very fragmented Android space.
Updates, patches and more.
An Android version is normally supported for 2-3 years by Google, which means that if there are security leaks or vulnerabilities identified in a supported Android version Google will fix it. After 3 years Google stops delivering security patches and after 2 years major updates. A (security) update or a new version must be tested and approved by a phone vendor, and this will shorten the period that a version is supported.
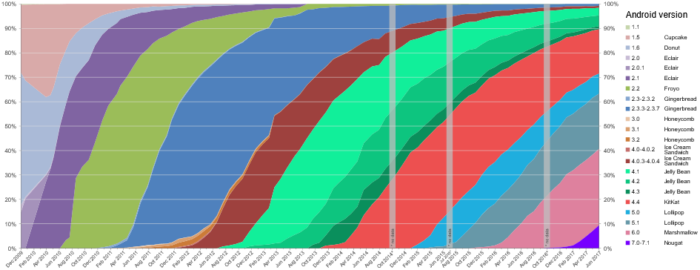
By Erikrespo [CC BY-SA 3.0 (https://creativecommons.org/licenses/by-sa/3.0)], via Wikimedia Commons
How can we solve this?
Do we need to standardize to for instance Samsung devices so that you can use Samsung Knox and Knox Mobile Enrollment and don’t allow BYOD anymore? If you ask me that is not a solution, the solution needs to come from Google itself. In the last couple of years Google woke up and started investing big time in services like Android for Work (Android Enterprise), Google Play Protect, Android Enterprise Zero-touch enrollment. Those services can be used on the majority of the Android devices and can be used as a standard in your environment.
In the next blogs in this series we will have a look at how we can solve or mitigate most issues we have seen with managing Android devices. If you ask me, when managing Android devices purely with MDM is become legacy and we need to redo our homework. (if not already done)
Great resources when managing Androids;
- Ignite 2017 session by Chris Baldwin and Derrick Isoka about Android and iOS devices
- Microsoft Intune Uservoice with Android related items
- Android version history
[…] my last blog we looked at managing the legacy Android devices, like mentioned Google is investing in making Android safer and more enterprise ready. Yesterday […]
[…] Androids in the enterprise a blessing or nightmare part 1 […]
[…] Androids in the Enterprise, a blessing or nightmare? – part 1 […]
Nice blog about Android Enterprise. I also read an interesting blog about Android enterprise published in MobiLock MDM blog.